Category: Compliance, Privacy & Security
This category explores the intersection of legal and technical considerations surrounding data protection and cybersecurity. The topics aim to provide valuable insights for businesses, IT professionals, and individuals on navigating the evolving landscape of compliance, privacy, and security.
Even Computers Get Viruses—Cybersecurity and Healthcare
Struggling with Price Transparency? You’re Not Alone.
Payer Price Transparency – Easily Provide Pricing Information Online
Payer Price Transparency by Quadax
Ensure Compliance with CMS Payer Price Transparency Rules
Quickly deploy secure, compliant and user-friendly web pages where patients can interactively explore shoppable services and create personalized estimates.
MIPS Scoring for Facility-based Pathologists: 3 Things You Need to Know
There are two pathways under the Quality Payment Program (QPP): MIPs and Advanced APMs. Unless you qualify as a participating clinician in an Advanced Alternative Performing Model, MIPS will be your default. MIPS has four weighted performance categories, identified below. This post will focus on Quality and Cost.
- Quality
- Improvement Activities
- Promoting Interoperability
- Cost
As a facility administrator, navigating the requirements to be successfully compliant with MIPS can be confusing, especially for those CMS considers non-patient facing clinicians, like pathologists. Pathologists must optimize their participation in order to minimize the risk of losing out on bonus opportunities stemming from new and evolving CMS payment models. One of those models centers on the new policies of Facility-Based Measurements. As a facility administrator, what do you need to know?
1. Definition of facility-based
Individual Facility-based clinician
• Must have 75% or more of covered professional services in any of the following:
◽ Inpatient hospital (POS 21), or
◽ On-campus outpatient hospital (POS 22), or
◽ Emergency room (POS 23), and
◽ Have at least one service billed with POS 21 or POS 23
Facility-based group
• At least 75% of MIPS-eligible clinicians billing under the group’s TIN are identified as facility-based.
Attributed to a facility with a Hospital VBP score
2. Your facility-based status
The easiest way to determine and confirm your 2019 Facility-based status is to start with CMS by utilizing their online MIPS eligibility and look-up tool, found at https://qpp.cms.gov/participation-lookup. (You will need your HCQIS Access Roles and Profile System (HARP) credentials, Tax Identification Number (TIN) and National Provider Number (NPI).) This tool will also inform you if you are exempt from MIPS, in which case, you will not be responsible for MIPS reporting. If you are not exempt, the tool will provide you with any special status needed for reporting other than facility-based. The tool will also indicate your attributed facility if you have facility-based status.
If you are a facility-based pathologist or group, CMS will automatically assign you Quality and Cost scores for based on the attributed facility’s Hospital Value-Based Purchasing (HVP) program. CMS will assign these scores even if you are not a patient-facing clinician.
Facility-based pathologists should attest to Interoperability Activity scores separately to maximize their MIPS score. Facility-based pathology groups must attest to these scores separately from the facility in order to be assesses as a group and to maximize their MIPA score.
3. Your potential 2019 MIPS performance
You can preview your Quality and Cost scores on the QPP website for estimated 2019 MIPS performance period, based on 2019 Hospital VBP Total Performance Scores (TPS) mapped to 2017 performance QPP data.
The 2019 MIPs scores will use 2020 Hospital VBP scores mapped to QPP data from the 2019 performance period. Note, scores between the preview and 2019 MIPS may change. How? There could be changes in the hospital to which the clinician or group is attributed. There could be updates to the HVBP TPS between 2019 and 2020 at the attributed hospital. Or, there could be updates to the distribution of MIPS quality and cost performance scores. The College of American Pathology suggests you may want to report on MIPS separately if you are not confident in your hospital’s VBP score as CMS will take the higher score from your reporting data.
The CMS recommends that eligible professionals check with the QPP Help Desk for more information on measures and the QPP.
QPP Help Desk Contact Information:
7:00 AM–7:00 PM CT Monday – Friday
email: QPP@cms.hhs.gov
Phone: 866-288-8292
*Adapted from Facility-Based Measurement: A Practical Overview, by Emily E. Volk, MD, MBA, FCAP (Aug 2019).
How Are You Sleeping Since the AMCA Breach?
Once upon a time, news of PHI disclosures or healthcare data breaches only caught the interest of security and privacy nerds. Now they grab headlines and prompt worries and distress among practice owners, privacy officers, CFOs, and patients alike.
The disastrous data breach of the collection firm American Medical Collection Agency (AMCA) is the latest to cause sleepless nights, particularly since, after the count of US citizens affected by the breach exceeded 20 million, actions by AMCA clients left AMCA no choice but to file for bankruptcy protection.
What made this breach especially scary to providers is that their patients’ data was exposed due to the actions or inactions of a vendor they assumed they could trust.
Since the AMCA breach, some Quadax clients have contacted us to learn whether or not we have been impacted by this event. In this article, we’d like to assure our audience that 1) we have no relationship with AMCA, and 2) we do have strong controls in place to protect our clients’ data both for our systems and for the third parties with which we contract for ancillary services.
As much as we’d like to tell you that you will never experience this kind of failure when you trust Quadax, we must admit that there is nothing in the world that will ever be completely hack-proof. As soon as something is ‘hacker-proof,’ the universe builds a more devious hacker. For that reason, Quadax never stops working at security and privacy; it’s never a box to be checked ‘finished’ so that we can move on to other matters.
Security is a full-time, never-ending endeavor. Three of the facets of the Quadax security efforts germane to this discussion are:
- Our SOC 2 Report
- Our extensive (exhaustive) vendor vetting program
- Our perpetual security monitoring program, including penetration testing, resource utilization monitoring, and routine vulnerability assessments
SOC 2
Quadax submits annually to audit processes to produce the System and Organization Controls (SOC) for Service Organizations Report Relevant to Security, Availability, Processing Integrity, and Confidentiality Principles. Each year, our external auditor conducts an examination of Quadax controls in accordance with attestation standards established by the American Institute of Certified Public Accountants. Their determination affirms that our controls were suitably designed and are operating effectively to meet the Applicable Trust Services Criteria throughout the specified period of time.
Vendor Vetting
Among the controls and processes examined by our auditor is Sub-Server and Vendor Management. Quadax maintains a stringent Vendor Management program that begins with initial vetting and carries through to annual assessments to ensure ongoing reliability and integrity. The Quadax Compliance and Legal departments collaborate on the process, with input from the Security Officer.
The vetting methodology proceeds through stages of assessment as data is collected, attestations are reviewed, and a number along a scale is assigned to indicate the “critical level,” reflecting the degree of risk the engagement represents to security and privacy.
Baseline verifications include:
- General Service Administration (GSA) System for Award Management (SAM) database: Is the vendor in good standing, or has the vendor for any reason been excluded, sanctioned, or debarred by a Federal agency?
- Office of Inspector General (OIG) List of Excluded Individuals and Entities (LEIE): Is the vendor in good standing, or has the vendor for any reason been excluded from participation in Medicare, Medicaid, and other Federal health care programs?
- Has the vendor been placed under a Corporate Integrity Agreement?
- Does the vendor appear on the Health & Human Services (HHS) “wall of shame”?
From there, collection of key data points helps Quadax to establish the critical level of the potential vendor through a thorough understanding of how the vendor will be operating: precisely what access is required; whether or not PHI will be stored, transmitted, processed, or accessed; whether or not there would be any offshore components; and several other important factors.
Third-party attestations to the compliance and operating standards of the vendor are also examined. Quadax requires that vendors provide either SOC 2, ISO 27001, or EHNAC, and potentially also PCIcompliance, as applicable.
Legal documents governing the relationship between Quadax and the vendors with which it chooses to engage, each carefully stipulating services, requirements, and penalties for nonconformance, will include some or all of these, depending on the nature of the services and the critical level assigned:
- Business Associate Agreement
- Non-Disclosure Agreement
- Vendor Insurance Standards Agreement
- Vendor Security Standards Agreement
- The Master Service Agreement (MSA) Agreement
Quadax leaves no stone unturned when it comes to safeguarding data and reputations – our own, and our clients’.
Security Monitoring
On a continual, ongoing basis, Quadax uses logging and monitoring software to collect data from system infrastructure components and systems to monitor system performance, potential security threats and vulnerabilities, to evaluate resource utilization, and to detect unusual system activity. Key indicator reports, along with other tools, serve to alert management of deviations from expected activity which may signal unauthorized access attempts. Quadax separately conducts routine vulnerability assessments on the corporate infrastructure, searching for any potential weaknesses that could be exploited so they may be mitigated before it’s too late. It’s important for vulnerability testing to be part of standard, regular routines since weaknesses may arise in any number of circumstances: through the installation of a new patch that corrects a different problem; through the implementation of a new application or an upgrade to an existing one; or through the introduction of a new client or vendor access channel, to name just a few.
It’s expensive and resource-intensive to maintain this degree of vigilance, but as a company entrusted with protected health information (PHI), personally identifiable information (PII), and confidential business information, we make security and privacy a top priority. You can read more examples of the serious commitment Quadax makes to compliance on our website.
If you’re not currently working with Quadax, but you’d like to learn more about our compliant revenue cycle solutions for hospitals, laboratories, or physicians and other professional providers, please get in touch. We’re always pleased to demonstrate how our services can help healthcare providers thrive despite today’s complex reimbursement environment.
FASB ASC 606: Prepare Your Laboratory for a Successful Transition
This white paper is to help clinical laboratory companies successfully implement the new revenue recognition accounting standard – FASB ASC 606.
Considerations for Private Companies Implementing ASC 606 Revenue Guidance – Part 2
Part 2: Audit Requirements
To assist private companies in understanding what the auditors will request and review, we have identified some of the relevant auditing standard requirements below.
Management’s implementation plan and documentation
Management’s implementation plan encompasses many activities—scoping, accounting assessment, solutions development, and other activities. Auditors need obtain an understanding of this plan.
From a scoping perspective, management is expected to have a variety of key processes and controls implemented to identify revenue streams, relevant contract components and features and business practices to support their accounting policy conclusions. Auditors need to understand how management selected contracts to validate the contract components and features identified during the initial scoping phase. Auditors will also need to perform testing to validate management’s assessment in order to provide support to the audit opinion.
From an accounting assessment perspective, the auditing standards require the auditor to obtain an understanding of the entity’s accounting policies including the reasons for any changes in these policies. To do so, auditors will be reviewing management’s documentation to determine if the accounting policies comply with ASC 606, and validating that the company’s accounting complies with those policies.
Internal control considerations
The auditing standards require the auditor to obtain an understanding of company’s internal controls relevant to the audit. Further, the auditor must evaluate the design of the controls and determine whether they have been implemented by performing procedures in addition to inquiry of the entity’s personnel. As a result, management must evaluate how any changes due to the implementation of ASC 606 impact its control environment.
Further, the new guidance requires management to either recast prior-period financial statements presented for comparative purposes (full retrospective method) or record a transition adjustment and provide disclosures of significant changes by financial statement line item (modified retrospective method). Management must have controls and processes in place for either method chosen. Auditors must obtain an understanding of those controls and test to substantiate there is not a material misstatement.
Extensive new disclosures
The extensive new disclosures required by ASC 606 may require companies to update systems, processes, and controls used to develop disclosures. It is important to note that those companies that assert they will experience little or no impact to top line revenue due to adopting ASC 606 will likely still expend a significant amount of effort to comply with the extensive new disclosure requirements. The auditors will need to perform testing in order to substantiate the new disclosures and underlying information used to support those disclosures.
Management’s progress
It is important for companies to keep their auditors abreast of implementation issues and progress. The more communication the company and auditors have throughout the implementation process, the less likely it is that surprises will arise.
The following indicators may lead the auditor to conclude that management is behind or failing to execute their implementation plan and, therefore, may necessitate additional work:
-
-
- Inability of management to articulate the details of their implementation plan or make progress toward implementing that plan
- Lack of a detailed implementation plan and timeline
- Evidence that key deadlines from the timeline have been missed and that there are neither plans to catch up nor enough time to do so
- Poor tone at the top, including lack of involvement from those charged with governance
-
Where do we start?
A comprehensive implementation plan that includes the right people across the right functions is critical to a successful implementation of the new guidance. Companies should consider the following action items as they tackle ASC 606:
-
-
- Train employees across the organization on ASC 606, and allow employees to help identify impacts to their own functional areas (forecasting, employee benefits, tax, sales teams)
- Develop an overall implementation plan and timeline
- Evaluate competence across the organization, and consider hiring external service providers to assist with the implementation process, as needed
- Inventory all contracts with customers and identify key terms and conditions, as well as any deviations from those standard terms
- For areas of change between existing GAAP and ASC 606, identify cross-functional impacts to the organization (including tax impacts)
- Make any accounting policy elections and document new policies, as needed
- Document and implement any internal control changes
- Identify disclosure gaps that require system updates or changes, and initiate the process to close those gaps
-
“One of the biggest takeaways we hear from public companies is not to underestimate the amount of time required to complete the implementation of ASC 606. Because the new guidance touches so many areas of the business, the implementation requires extensive coordination across functional areas which, of course, takes time and effort.”
Cullen Walsh, Partner
Grant Thornton Accounting Advisory Services
Want to learn more about how ASC 606 can affect your organization? Join Cullen Walsh, Partner, Accounting Advisory Services at Grant Thornton and Walt Williams, Director of Revenue Optimization and Strategy at Quadax, as they present, “ASC 606 – Lessons Learned and What You Need to Know” on Tuesday, November 27 at 2:00 p.m. EST.
Register For Webinar
For more information on how Grant Thornton can help your company, contact your GT Audit Partner Daryl Buck, Cullen Walsh, Matthew McCleary, Chris Stephenson, or your local GT service provider.

“Grant Thornton” refers to Grant Thornton LLP, the U.S. member firm of Grant Thornton International Ltd (GTIL), and/or refers to the brand under which the GTIL member firms provide audit, tax and advisory services to their clients, as the context requires. GTIL and each of its member firms are separate legal entities and are not a worldwide partnership. GTIL does not provide services to clients. Services are delivered by the member firms in their respective countries. GTIL and its member firms are not agents of, and do not obligate, one another and are not liable for one another’s acts or omissions. In the United States, visit grantthornton.com for details.
© 2018 Grant Thornton LLP. All rights reserved. U.S. member firm of Grant Thornton International Ltd
Considerations for Private Companies Implementing ASC 606 Revenue Guidance – Part 1
By: Grant Thornton LLP (Special Guest Post)
As the effective date for the new revenue guidance in ASC 606, Revenue from Contracts with Customers, quickly approaches for many private companies (January 1, 2019 for calendar-year companies), management and audit committee members are faced with many questions.
- What lessons have been learned from public companies’ implementation of the new revenue standard?
- What will my auditor be looking for?
- Where do we start?
This blog addresses these questions and serves as a conversation prompter to help executive management engage with those parties involved in the implementation process.
Remember, implementing the new revenue guidance is not just an accounting exercise. The implementation process is a cross-functional exercise that requires coordination between tax, sales, and information technology (IT), among other functions.
“Even companies that are not expecting a material change in revenue must undergo an exercise to identify gaps between existing accounting and ASC 606, determine if any changes need to be made (including system changes), implement the changes, and document the analysis for the external auditors. This process can be time-consuming and require significant effort.”
Daryl Buck, National Managing Partner
Accounting Advisory Services
What lessons have been learned?
As public companies are in the process of finalizing their ASC606 implementations, we can share some “lessons learned” from observing the implementation process and interviewing those overseeing the implementation process.
Get the right people involved, earlier rather than later
Because of the pervasive effect of the new guidance on an organization, management must identify the right stakeholders to provide input into the implementation process. Not only does a company need to identify the right people within the organization to provide input (sales teams, IT, tax), but a company should not hesitate to engage external professionals where assistance is needed (training, technical accounting expertise, IT changes, etc.). Getting the right team in place from the start is key to a successful implementation.
Do not underestimate the effort required to inventory contracts
One of the first implementation tasks for many companies is to inventory their existing revenue contracts, identify standard terms and conditions, then determine if any contracts deviate from those standard terms. For companies that allow sales teams to deviate from standard contract wording, this process can be time consuming and require extensive communication and coordination.
Allow extra time for key contract terms
The new revenue guidance requires companies to evaluate their existing arrangements against the new five-step revenue model. This analysis may be straightforward for some contracts, but if your contracts include any of the following provisions, plan to spend extra effort and time to address these provisions and document your analysis:
1. Multiple goods or services — Performance obligations are the unit of account for applying the new revenue standard, so determining the appropriate performance obligations in a contract is critical to how a company will recognize revenue. The criteria for identifying performance obligations are new and therefore companies need to take a fresh look at their goods and services and assess them against the new criteria.
2. Variable consideration (meaning any consideration that causes the transaction price to vary) such as retrospective volume discounts, rebates, bonuses, or penalties — The new revenue standard generally requires companies to estimate these amounts for purposes of determining the transaction price and evaluate whether to constrain the amount of estimated variable consideration to ensure that revenue is recognized only to the extent it is probable that a significant reversal in cumulative revenue recognized for the contract will not occur when the uncertainty is resolved.
3. Material rights (for example, a prospective volume discount that is incremental to the range of discounts typically given to a particular class of customer in a geographical area or market) — Under the new model, a company must account for a material right as a separate performance obligation and this may require a complex accounting exercise to allocate a portion of the overall transaction price to the material right performance obligation.
4. Modifications — ASC 606 includes prescriptive new guidance for modifications and this has necessitated some companies to implement system solutions to track and account for these modifications.
5. Contract costs — The new revenue standard introduces guidance for costs incurred from a contract with a customer, which has been codified in ASC 340-40. Companies are required to capitalize certain costs under this new guidance and therefore companies that may have elected to expense certain costs in the past may experience a change under the new guidance.
6. Customized goods — Companies that produce customized goods and have an enforceable right to payment for work completed to date may experience a change in accounting as the new guidance requires the company to recognize revenue as it performs the work, that is, over time (rather than at a point in time).
Do not forget about disclosures
Private companies may be spared from some of the new, extensive disclosure requirements that public companies have to comply with, but private company disclosures will still require significant time and effort. Private companies must disclose disaggregated revenue information, information about performance obligations, and significant judgments in determining the timing of satisfying performance obligations and in estimating variable consideration.
Watch for Part 2 of this blog series addressing audit requirements and considerations on November 13.
Want to learn more about how ASC 606 can affect your organization? Join Cullen Walsh, Partner, Accounting Advisory Services at Grant Thornton and Walt Williams, Director of Revenue Optimization and Strategy at Quadax, as they present, “ASC 606 – Lessons Learned and What You Need to Know” on Tuesday, November 27 at 2:00 p.m. EST.
Register For Webinar
For more information on how Grant Thornton can help your company, contact your GT Audit Partner Daryl Buck, Cullen Walsh, Matthew McCleary, Chris Stephenson, or your local GT service provider.

“Grant Thornton” refers to Grant Thornton LLP, the U.S. member firm of Grant Thornton International Ltd (GTIL), and/or refers to the brand under which the GTIL member firms provide audit, tax and advisory services to their clients, as the context requires. GTIL and each of its member firms are separate legal entities and are not a worldwide partnership. GTIL does not provide services to clients. Services are delivered by the member firms in their respective countries. GTIL and its member firms are not agents of, and do not obligate, one another and are not liable for one another’s acts or omissions. In the United States, visit grantthornton.com for details.
© 2018 Grant Thornton LLP. All rights reserved. U.S. member firm of Grant Thornton International Ltd
Three Ways Providers Can Prepare for MBI Impact
March 12, 2018 By: Quadax
***UPDATE: Commencing January 1, 2020, Providers must submit claims to Medicare with the Medicare Beneficiary Identifier (MBI) regardless of the date of service.***
Beginning January 1, 2020:
- Medicare will reject claims submitted with the old Health Insurance Claim Numbers (HICNs) with several exceptions.*
- Medicare will reject all eligibility transactions submitted with HICNs.
- Customer service representatives on the phone will not be able to identify patients using the HICN.
- Since the MBI has more alpha characters than the HICN, CGS suggests using their tool to convert the MBI into characters to use on the telephone number pad for IVR inquiries before calling. The tool can be located here. Other MACS have a conversion tool, too.
- The MBI will not be on the Medicare Summary Advice or 835 if the HICN was submitted on the claim and the claim denies for submitting the claim with the HICN.
If you do not use MBIs on claims on and after January 1, 2020 you will receive:
- Electronic claims reject codes: Claims Status Category Code of A7 (acknowledgment rejected for invalid information), a Claims Status Code of 164 (entity’s contract/member number), and an Entity Code of IL (subscriber)
- Paper claim denial codes: Claim Adjustment Reason Code (CARC) 16 “Claim/service lacks information or has submission/billing error(s)” and Remittance Advice Remark Code (RARC) N382 “Missing/incomplete/invalid patient identifier”
Railroad Medicare beneficiaries will have the same format of numbers and will not be identifiable by their MBI. The patient cards will have a Railroad Retirement Board logo on them.
Medicare Advantage plans have their own subscriber identification numbers which are not MBIs.
*For more information, see the MLN Matters Article.
Original 10/7/17 post: The transition to Medicare Beneficiary Identifiers (MBIs) will universally impact the world of healthcare. Given the sheer volume—150 million MBIs assigned to 60 million active and 90 million archived beneficiaries—the magnitude and foundational nature of this change could potentially affect when and if providers’ receive payment. Being prepared for the MBI transition is a provider’s best strategy.
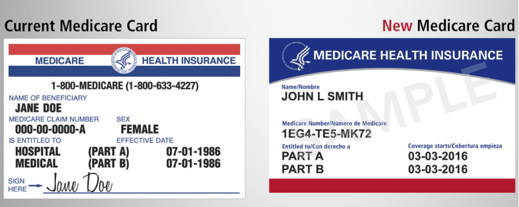
Starting April 2018 and running through April 2019, Centers for Medicare & Medicaid Services (CMS) will begin issuing new Medicare cards to beneficiaries. On the new Medicare cards, the current Health Insurance Claim Number (HICN) will be replaced with an MBI—a unique, randomly generated number.
When planning your MBI transition strategy, consider the impacts of rollout, data capture, and random-generation on your billing system, office procedures, and automation logic.
Lengthy MBI Rollout
This is not a flip-the-switch transition. With a year-long rollout, the affected population will present a mix of the old Medicare cards and the new. Your billing system and your patient-facing procedures will need to accommodate both. Once the rollout starts, a patient may have claims active that were submitted with an HICN and other newer claims submitted with the new MBI. Your system will need to track both, during the rollout and after, for the full length of your reimbursement cycle for each claim. When filing appeals, CMS is asking providers to use the beneficiary identifier (MBI or HICN) that was used to submit the original claim.
Capturing MBI
One of the biggest challenges for providers in making this change will be getting the new MBIs. Providers will need to get the information directly from patients. The goal is for each beneficiary to provide their new Medicare card at the first visit after the new card was issued. As a result, the best method for capturing MBI will be during your patient eligibility verification procedures. Patient communication before and during the transition is key.
 Start communicating with your Medicare patients now so that they will know what to expect. Train staff so they will be prepared to answer questions about the change, the timeline, and what patients need to do. CMS Medicare Card Messaging Guidelines provide guidance on how to talk with Medicare patients about this change.
Start communicating with your Medicare patients now so that they will know what to expect. Train staff so they will be prepared to answer questions about the change, the timeline, and what patients need to do. CMS Medicare Card Messaging Guidelines provide guidance on how to talk with Medicare patients about this change. Then, beginning April 1, 2018, start reminding Medicare patients to bring their new Medicare card to their appointment. Consider adding this reminder to your appointment notice sent to Medicare patients a few days before their scheduled date of service.
Then, beginning April 1, 2018, start reminding Medicare patients to bring their new Medicare card to their appointment. Consider adding this reminder to your appointment notice sent to Medicare patients a few days before their scheduled date of service.
If the patient has forgotten to bring their new Medicare card, CMS has just announced that starting in June 2018 providers will be able to look up a Medicare patient’s new Medicare number through their Medicare Administrative Contractor’s (MAC’s) secure web portal. If you do not have access to your MAC’s portal, CMS is recommending that you sign up now. And starting in October 2018, through the transition period, CMS will return both the HICN and the MBI on every remittance advice when providers submit a claim using a patient’s valid and active HICN.
MBI random-generation Effect on Automation
Being randomly-generated, the new MBI 11-digit character string will not be formatted with built-in intelligence. The old Medicare number (HICN) was formatted so that certain values in certain positions within the HICN character string had meaning. Any process referencing the Medicare number’s character string for values to drive automation, will need new programming logic and/or procedures. The Railroad Retirement Board (RRB) is an example of this. It will not be possible to identify from the MBI if patients are eligible for Medicare because they are railroad retirees. Only through a visual inspection of a patient’s Medicare card and seeing the RRB logo in the upper left corner, and “Railroad Retirement Board” at the bottom, will providers be able to identify and manually capture this information. Consider how this will impact your data capture strategies. If you are not already doing so, you may want to include the scanning of insurance cards to your patient eligibility verification procedures.
Be Prepared!
MBIs will begin to hit your office and systems April 2018. Make sure you and your vendors are ready by April 1st—no fooling! Visit Quadax RESOURCES to stay informed about future developments on the MBI transition.